The Risk Management process – 5 Key Steps

This article outlines the well-documented stages of risk management with examples of application within the security remit.
This risk management approach follows five key steps. Different names can be applied to them depending on the source being read; essentially, they are the same. The steps are as follows:
- Identify the risk
- Analyse the risk
- Evaluate the risk
- Treat the risk
- Monitor and review the risk
As a security professional, before you dive into these steps it is important that the risks being faced are put into context for the activities you are providing protection for. I like to consider these under the following criteria:
- Day-to-day (Normal risks)
- Event Specific (Bespoke requirements)
- Reactionary (Risks faced in returning operations to normal)
This is set from understanding your baseline factors and what needs to be considered from your established risk assessments or threat and vulnerability reviews.
To establish the context, it is necessary to understand your security’s objectives and operating environment. This will then influence the five steps and how you apply these to mitigate the risks in front of you. Remember though, there will always be the potential unknown or sudden impact situation that changes your risks and subsequent response plan. These can be difficult to deal with; however, the five steps applied and reviewed as necessary will always be the building blocks from which to respond.
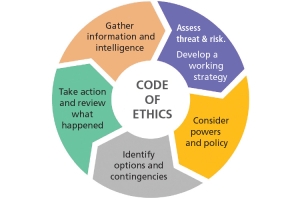
Apply this in line with the National Decision-Making Model (NDM) throughout the incident to review and amend the responses; it works well in partnership with these five steps.
Objectives to risk management can be either explicit – well defined, and clearly outlined; for example, we will reduce theft by (x)% through increased security engagement – or they are implicit – for example we must follow legislation or legal requirements. I mentioned your baseline factors; these include stakeholders, assets, environment, occupiers, profile of targets etc. – anything that poses risks to our protective responsibilities. These will be a consideration of your objectives.
National Decision-Making Model
Step 1: Risk Identification
The list you develop of identified risks within your risk and threat matrix needs to be flexible and to have considered the day-to-day, bespoke and reactionary criteria. These identify considerations that will have an impact on successful delivery of the security objectives: these are the risks. It is also important to consider the risk appetite of these: are some risks acceptable? Are some out of your control entirely? As security providers we can identify risks but have very little influence in rectifying them.
For example, the need for physical security at an entry point, or a faulty security tool that has been well documented, but ignored. Identifying these risks also needs to include a good understanding of their causes or sources. Good intelligence is essential in developing this identification of risk(s).
Step 2: Risk Analysis
Risk analysis establishes the potential impact of each risk and its likelihood of occurrence. You would have all seen these scores in various guises. What is important to remember is that these are subjective to the applied area of risk, mitigation methods in place and key understanding of the baseline factors.
When analysing the risk, it is important to review previous incidents, how these were these dealt with and whether learnings from historical events can be applied to give better mitigation to the current risk being faced. There are many ways in which the analysis can be depicted; heat maps, severity matrices, etc. In analysing risks, understanding is vital and to ask “why” when responding to incidents, especially when we consider who will be the front-line responders to these risks when they manifest.
Risks need to be assessed consistently, especially when they are shared across dynamic environments; for example, Publicly Accessible Locations (PALs). As with all risk management, good communication is required to ensure each stakeholder understands the severity of the risks within this step.
Step 3: Risk Evaluation
Risk evaluation determines the tolerability of each risk, or where these sit within the risk appetite. As mentioned before, as security providers we may have a limited influence on this. At what level a risk is acceptable is different from the severity, how tolerable a risk is places where it sits as a priority to how we respond. Comparing the severity as defined in the analysis, likelihood and eventual consequence decides whether this risk is acceptable or unacceptable, or to what extent the risk impact can be managed in the risk appetite. As an example, with PALs, we know that they will offer a fertile environment for hostiles or opportunistic crime, (for example, bag theft). While we do all we can to mitigate this, we know that it will happen and have to accept a certain level within the evaluation.
Decision making at the correct level will determine an informed risk acceptance within the parameters of the environment that we are protecting. This will support the decision making in responding to identified risks, their prevention and success in the objectives set out, if and when these risks are manifest.
Step 4: Treat the Risk
Risk treatment is the processes employed when responding to the risks and the evaluation that has already been defined – what systems or processes are already in place, what additional resources are required, additional attention to legislation etc. The risk treatment and final step 5 are where the NDM works in close partnership.
Both elements work in a cyclical manner. Risk treatment rotates around individual or combined elements to ensure they bring residual risks to a tolerable level; these are assessed continually to ensure acceptable levels are maintained or mitigation can be delivered. NDM ensures that the incident or situation’s information is available, is assessed within the operational parameters, reviewed for options to meet adaptability, and appropriately responded to.
Ideally, and under suitable planning, risk treatment needs to consider: eliminating the risk entirely (appreciated that this is not always possible); removing the source of the risk (again not always within our powers as a security provider); sharing the risk; accepting the risk, but under the objectives we have set out and modifying any control measures to affect the likelihood or outcomes of the risk.
In all elements of risk management communication is paramount, and in most incidents the first element to fail. We have all experienced those incidents where radios fail; when you most need a phone signal, you don’t have one; messages transmitted under duress that cannot be clearly understood etc. Therefore, within the treatment of risk ensure communications are a top priority.
Step 5: Monitor and Review the Risk
Risks will change over time and as events or operational dynamics change, so the risk needs to be constantly reviewed and monitored. I have mentioned in previous risk management articles that the correct knowledge at the right level and in the right place is essential in dealing with the risk. Taking the NDM into consideration at this stage allows the information to be part of the process and the ability to have the right person in place and (ideally) at the right time. Monitoring risks and the mitigation of them is dynamic; being flexible in dealing with these is integral to successful risk management.
Being aware of changes in the environment, new or developing risks, and where possible, as much intel as is available to guide our responses through continual assessment, is vital.
As experienced security professionals, especially those that manage established contracts, we will do this instinctively due to inherent familiarisation and experience. New environments will always be more challenging, hence making sure risk and threat reviews are continuously employed in establishing operational parameters. Experience has shown that monitoring allows time to prepare.
Granted, some critical incidents may be a minute-by-minute response; however, there will be a time when an opportunity to review occurs. Then step 5 in line with the NDM will be necessary and beneficial.
Overall, the above steps are the foundation blocks to risk management; they are well documented and can be reviewed across many sources. How they are applied depends on our individual approaches, experience, working environments and as mentioned, often under an external influence and operational parameters. There will always be unique changes to the environments where we operate. As such we need to ensure that the results, observations, mistakes, and good practice are recorded and, most importantly, shared with responders and stakeholders alike.
Jon Felix BSc(Hons) MDIP MBCI MSyl
Risk and Threat Advisor
CIS Security