Data Centre Security: The bits not to miss
Data and data networking is effectively a utility supply to us all and no different to other public utility services in terms of our dependence on it. Data centres and fibre routes are the medium for all data. They are relied on by the public, governments, the military, industry, the financial sector, scientists and researchers, and the healthcare sector. Society is becoming more and more reliant on data and so interruption to data centre services and networks can be catastrophic if resilience and security systems are not commensurate with the value of the data.
As a result data centres are by their nature becoming more vulnerable to both physical and cyber attack as technology progresses.
Security levels vary significantly depending
on the sector or business that an organisation operates in. Assessing appropriate levels of security for a facility requires strong stakeholder presence and the knowledge and expertise brought by consultants and supply chains with strong track records.
This article provides a starting point for firms looking at the security of their existing or proposed data centre facilities.
The aim of a security strategy, as a minimum, will be to achieve the following:
- security installations should protect to a level commensurate with the current and future risks assessed by an organisation
- a tenable, sensible solution that is neither under designed nor over designed
- takes into account the organisation’s strategy for the future (for example: rate of expansion, diversification, sale, merger)
- avoids expensive and disruptive retrofitting by addressing all requirements at strategy stage, not leaving them until build stage
- is not so complex to utilise that optimum performance is rarely achieved
- achieves an acceptable solution to all stakeholders, recognising that stakeholder requirements often differ
- recognises that interruption to data centre services is more commonly from within an organisation, either accidentally or maliciously
- is achievable within the capital and operational budget available, a budget commensurate with the value of the data centre to the organisation
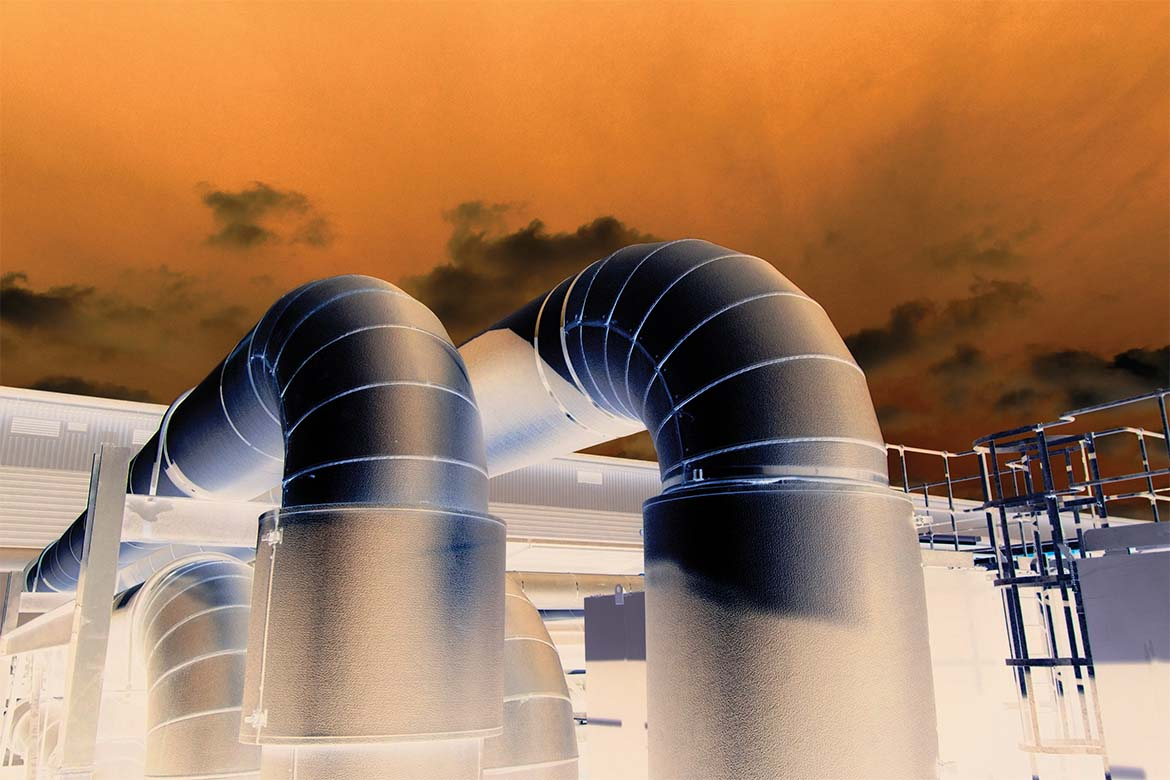
A volume of data can be looked at as an electrical power requirement. For example, emails sent and received, data processed and data storage is achieved via a server and a network. In simple terms the server and network require electrical power to run, and chilled air to prevent servers overheating. Electrical power is also required to produce the chilled air. What is the relevance of this to security design? If the electrical power or chilled air supplies are cut, the server will shut down. This can have an impact on the running of an organisation and in extreme situations could incapacitate it.
Therefore, in the design, construction and operation of data centres there needs to be a robust security strategy in place to protect the information and server operations contained inside the data centre, and to protect the staff within and the facility itself. A security system aims to maintain data flow and storage, protect processing power, prevent damage or loss of data, and prevent theft of data.
The principal areas of risk in and around data centres, that become security risks, include the following:
Interruption to electrical power or cooling
Resilient power and cooling systems are built into data centres to provide redundancy. The effectiveness of this resilience is down to engineering design. For power, resilience is provided by the use of dual power feeds, UPS systems and standby generators, as an example. The same with cooling, back up cooling plant is provided. These systems, which are computer controlled, must be protected both physically and the control systems protected to prevent the lifeblood of the server being interrupted.
Unauthorised access to the facility and data halls
Unauthorised access to a data centre is prevented by a multitude of precautions. One of the challenges is that operatives needing to work in the data centre will include not just the full-time staff, but also external contractors. Precautions may include: physical guarding services; double perimeter fences with motion detection and cameras; separate access and egress routes to simplify security operations; secure access to data halls including mantraps and biometric control; cameras located to monitor and record technician access to every server, power and fibre network, or to plant; computer controlled door locks; camera covered door and zone access.
High impact physical attack
This may include vehicular, airborne or other types of impact or explosion. Precautions can include: subterranean construction of the whole facility; a blast proof external envelope to the building which may include reinforced concrete walls and roof; blast proof zones within the data centre as a precaution against incendiary devices internally; road-blockers or similar measures to prevent unauthorised vehicular access; dock-levellers to negate the need for vehicles to enter the facility.
Technology risks and cyber attack
The technology security side of data centres is a substantial subject in itself. Cyber attacks are probably the most significant concern to many organisations, especially those considering the Cloud. Vulnerable are not just servers but also the electrical or environmental control systems in the facility. Technology departments expend significant resources on software and research in this field.
Attacks on services outside the curtilage of the facility (eg fibre routes)
Because access to fibre routes that link an organisation’s facilities is outside the curtilage of each facility, it is more challenging to fully protect. Whereas data is often encrypted or scrambled after it leaves, or before it enters a facility, the risk is more the physical severing of a route, either by accident or maliciously.
Fire
Fire protection systems are sophisticated and extensive within data centres, to protect the occupants and every element of the facility. Technology is advancing to limit fire suppression to the precise zone in which it is activated, without damaging plant and equipment, and often allowing continued service of the facility.
Site location security
This will be addressed at due diligence stage when choosing a site. Depending on the nature of the data centre some organisations may avoid the following sites:
- under flight paths to airports
- sites adjacent to rivers, lakes and flood plains
- sites very close to train lines
- countries with perceived political stability issues
- areas where there is significant seismic activity or a history of natural disasters or weather damage
- areas adjacent to fire or explosion risks (eg adjacent to particular types or industrial or storage facilities)
Often sites are located away from public view and main roads. Data centres are often without signage and anonymously located. It is not uncommon to utilise old military bunkers, disused open cast mines or to build underground.
To conclude
The most secure data centres are generally those that organisations build for themselves. Although it is interesting to note that in line with current outsourcing trends corporates and public organisations increasingly outsource their data centre requirements to hosted data space with co-location providers. The level of security in these facilities has increased markedly over recent years and if projects are specified, designed, managed and delivered well, the security levels can be on a par with facilities that organisations build for themselves.
Security installations within data centres have complex interfaces with many of the building’s mechanical, electrical and other systems. The complexity is often under-estimated and the integration with the rest of the building project inadequately planned. This results in abortive work and impacts on cost and programme. It is therefore important to involve appropriately experienced security professionals, stakeholders and consultants from the outset of a strategy for a data centre build, to avoid such project delivery issues.
Gavan Mackenzie
Managing Director, sineQN